hi in this lecture and in the next one we’re going
to be talking about banking and payment security this is a really important issue for the security
engineer because an awful lot of the attacks that happen on systems are after the money and we
have to understand how things like online banking um and credit cards and even cryptocurrencies work
because these are the mechanisms for fraud and the targets for fraudsters so we already talked
a little bit about bank security in the first couple of lectures we looked at bulk compromise
how espionage agencies try and get hold of back information at scale in order to do
surveillance of target populations there’s also bulk compromised by crooks who for example
may try and get lots of personal information from one bank say from the register of anti-money
laundering information that people have given so they can use it to open accounts elsewhere and
there may be whistleblowers who are trying to tell journalists about bad things
being done by famous people now there are also more targeted attacks
where a journalist might be after information about a celebrity a rock star politician or
whatever and these are generally controlled by internal controls in the old days that meant
limiting information on customers to the branches where their accounts were canned and nowadays
it generally means delegated authentication that the person in the call center
can’t see your account information until you’ve answered a few security questions so
the internal controls also work against insider fraud against insiders helping themselves to your
money and moving it from one account to another but in this lecture and in the next one we’re
going to be concerned mainly with how do you stop external fraud against payment systems and our
goal is to understand the world payment systems and through that to get a
lens to understand cybercrime now here’s a very rapid history of banking if
you go back to the 15th or 16th century people used gold and silver coins and the merchants
would keep your assets in their vault for a fee and then after a while things evolved
so that you just hit a balance with them you give the gold merchant your 20 guineas and
he’d give you a receipt for the 20 guineas and you could go and get them back later and then
people added interest you had deposits loans mortgages various payment instruments that could
be used to finance business and to finance trade the next big innovation that came through was
paper money which was first seen by marco polo on a trip to china in the 13th century and that
gradually spread outwards from northern italy and by the time we get into the 19th century
we had a paper-based payment system with checks bills of leading all sorts of bits
of paper that flowed around the world and with them the money flowed too so
how did pepper best payments work well some countries including the uk still use czechs
although other countries have abolished them and a check is basically a written order to your
bank saying dear royal bank of scotland please pay alice a hundred pounds for my account
with you number one two three four sign bob so bob makes out this check on a check form
pulls it to alice she takes it to her bank they pay it into her account if her account is
clydesdale for example then the clydesdale will send those checks right into raw bank at the
close of day and they will all settle up now this was fine between mutually trusting parties
but the the system was problematic because of a scale and speed from the user’s point of
view it was slow it took three to ten days to to clear a check and during that time you had
a note on your account that there was a balance of an extra 100 pounds in your account but it wasn’t
cleared yet and so you might not be able to spend that money or if you were you could find yourself
with an unpaid overdraft of the czech bounced now checks sometimes did bounce either because
the the drawers account was out of funds or when the check was presented to the
drawer with their bank statement they said oh this signature is forced the whole process was
very expensive for banks and there were lots of different hacks in different countries to push
back on fraud and make the system more workable but by the time electronics came along this
was a system that was right for mechanization so how do banks send money well the simplest
case and the earliest case that was tackled was the case of sending money overseas because
that was particularly slow expensive and unsure in the old days and how things work is that
banks in scotland for example will have accounts at correspondent banks in other countries so
if you want to send your ant agatha in sydney and australia a thousand us dollars your bank
will send to national australia bank please pay australian dollars one thousand a d jones account
number xyz from our account with your number abc so this is a bit like a cheque only it’s drawn
on an account so that your bank in scotland hazard an account in australia so the technical
question now is how can you do this electronically well from the mid 18th century people invented
the telegraph samuel morrison america and charles wheatstone in britain got telegraphs going
domestically by various means and then from the 1860s we started to get international telegraph
cables thanks to lord kelvin who pioneered the thing by laying a telegraph cable across the
atlantic and the earliest users at scale among commercial firms were banks because it enabled
them to transfer money quickly and more cheaply and securely than with the old paper mechanisms
but the question then is how do you stop fraud because in an old-fashioned victorian
telegraph the messages went from one telegraph station to another where they were
copied by human operators so what was to stop a human telegraph operator intercepting a message
to the national australia bank and then making the payee one of his friends instead of your
aunt agatha well the answer was what was called a test key which was basically a manual crypto
hash now here’s a simple example but it’s not that much more simple than some of
the weakest systems that people used so what you would have is a table of um random
numbers um with uh and and here we have uh the rows are by thousands of currency units and
the columns um are by the mantissa there so if you want to authenticate 376 000 pounds
you look at the the thousands and that’s six so that’s 71 and you write down 71 you look at
the tens of thousands this is the second row that’s seven so that’s 29 so you write that
down you look at the hundreds of thousands um and um that’s three so that’s um 54 so
you write that down and you look at the millions and that zero so you write down 53
and you add them all up and this gives you 208 and you then send that along with the message now
in practice there were more numbers than this um the uh the better systems tended to have four
digit rather than two digit um random numbers in the table and the tables would be changed perhaps
once a year in order to make it more difficult for a cryptanalyst to figure out enough of
the values in the table in order to forge a telegram the system is still cryptographically
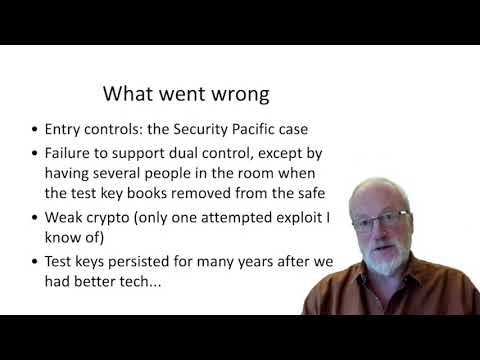
weak but it kind of worked for quite a while so what actually went wrong well um the most
famous attack on telegraphic transfer was in the 1960s the security pacific case where a bad person
at security pacific bank in in san francisco sent a telegraphic transfer for 10 million
dollars to a russian diamond company in zurich he’d arranged with them to buy 10 million dollars
worth of industrial diamonds and he sent this on a friday just before a monday that was a bank
holiday in america but not in switzerland so that he’d have time to hopefully get away and so
he basically used an internal code that was used within the bank to authorize um funds transfers
from the telegram room and the reason that this failed was that the internal procedures in the
bank didn’t support jewel control anybody could go to the telegram room and if they had the
appropriate authority which in this case was a password then the telegraph clerks would make up a
test key and send the instruction off and the only way you had jewel control in fact in the telegram
room is that there are several people in the room where the code books were and um so one one of
them would compute the code and another of them would test it but this didn’t stop internal
dishonesty now although the cryptography was weak there was only one attempted exploit that i
know of in this period where um the dictator of an african country attempted to send a 10 million
dollar wire transfer to himself and this failed because the whole country was in a one million
dollar overdraft limit but nonetheless um people realized that it was weak and they set about um
producing a replacement getting the replacement actually up and running took something like
20 years but the process started in the 1970s the replacement for the telegraphic transfer
system was put together in the 1970s by a consortium of banks who set up a jointly owned
company called swift the society for worldwide international financial telecommunications and
this was basically an early secure email system that enabled any one member bank to talk to
any other member bank and how it basically worked like this if you went into a branch of
the royal bank of scotland and sent to send a thousand us dollars to your bank agatha to to
up to your aunt agatha then the branch would send a message on its internal network to the rbs
headquarters in sight hill where they would have the room with the machinery which did swift and
swift had a set of cryptographic keys which had been exchanged with all the other banks with which
rbs did business worldwide so there would be a crypto key that had been exchanged with national
australia bank in sydney and rbs would then send a message with a message authentication code on it
so the swift regional general processor in london which would keep a log of the message that
had gone through the message would then be sent to swift’s headquarters with processing in
both belgium and the netherlands where it would be logged again and it would then be sent to the
regional general processor in australia which was down in sydney and that would then in turn send
it to the national australia bank’s headquarters where the message authentication code would be
checked so here you’ve got separate measures for integrity namely the message authentication
code and from non-repudiation namely the logging as for confidentiality that was an issue because
a number of countries at the time didn’t allow people outside government to use cryptography and
so sometimes the local link had to go in the clear key management that was done um
manually between senior bank managers because when the guy from rbs went out to
australia to set up a relationship with nab he might take a key with him in an envelope
and come back with a key from national australia bank in another envelope or they could send
it by post to each other’s domestic addresses swift also supported dual control in that while
clark a would enter transactions accountant b would check them and can change them and
then manager c would verify and release a whole batch without being able to change any
of them and so you’ve got jewel control between b and c both of whom would have to collude in
order to send a wicked message now swift at the time it was set up was owned by about 500 banks
and now it’s owned by 11 000 banks worldwide and it sends something like 125 trillion dollars
a year which is substantially more than world gdp but bear in mind when you hear such figures
that it’s the bank’s own systems that actually balance the funds and of course funds are
netted off at both ends so banks just have to settle up from time to time if their bank
accounts with each other gets out of kilter so how do you go about doing attacks on swift
well some of the sophisticated attacks have involved sending guarantees rather than cash
because if you can persuade bank a to give a guarantee to a customer of bank b then that
customer can borrow some money against the guarantee and make off with it and be long gone
by the time something is noticed whereas if you were to do an internal attack on bank a and
send money to bank b then the out of balance would be noticed within a day or two and um bank a
would be able to follow up and get the money back the second thing that we
learned with attacks on swift is that if an attacker can figure out how to
send money the hard part is in the laundry step there have been a number of cases where some
programmer at bank a put a message dishonestly into the swift message queue and then turned up
at a a bank in bangkok strasse in syria to collect the money and got promptly arrested because they
didn’t understand the difficulty of laundering money and they didn’t understand the context
and the kind of controls that you can expect to have fired up if you suddenly turn up and try
and take away 10 million dollars in a carpet bag now one of the most interesting large-scale
swift frauds that happened recently was in 2016 where the north korean government stole
81 million dollars from the bank of bangladesh they tried to steal quite a bit more and the full
story is in my book but the interesting thing here is that they managed to get away with some of
it at all and what they had done is arranged for their agents to set up in advance some
crooked deals through a casino in the philippines so that when the money arrived there there was
a chain of agents ready to launder it through further organizations that would be resistant to
law enforcement inquiries into money retrieval another aspect of attacks on swift is attacks
on confidentiality by law enforcement and intelligence agencies now before 9 11 this tended
to take the form of attacks on confidentiality on the local loop but since 9 11 the american
government basically demanded access to the entire swift message stream and after
some humming and hawing in the european parliament this was granted the americans are
particularly keen to track terrorist financing and to exclude iran so they can put on sanctions
and this has been one of the driving forces of the um behind the undermining of financial
confidentiality worldwide now we’ll come to that later when we start talking
about anti-money laundering controls the next component in the international
financial payment system is the credit card these started off in the 1950s in in new
york where dinos club and american express introduced cards so that people could
pay for restaurant meals and hotel stays and they spread slowly as an elite
product from one bank to another in the uk for example barclays introduced it
as the barclay card and it was a status thing if you’re a wealthy person to have a credit
card the other banks also introduced it and got in bed with mastercard which
was the competing global franchise this grew slowly because the difficulty in
getting any payment mechanism going is that not many people want to have your credit card
until there are lots of merchants who are accepted and yet merchants don’t want to go
to the trouble of putting acceptance machines of various kinds in all the stores until
enough of the prospective customers have got cards so that took about a generation to get going
until suddenly in the mid 1980s credit cards turned into a profitable mass market product
that’s the time when you could use a credit card in just about any store in the high street and
by then there was suddenly a race to add online authorization in the uk in order to cut the cost
of credit cards which previously had operated by imprinting a manual sales voucher which the
customer would sign a little bit like a check and we also rushed to add pins so that people could do
cash withdrawals from atms and of course the banks were happy to charge transaction fees and interest
as soon as you took cash out of your credit card what also happened then is that once credit
cards became a mass market product we started seeing credit card forgery and this was driven
initially in the far east where people figured out that you could get credit card numbers and
expiry dates from old sales vouchers or from carbon copies of virtuals that were discarded
in in rubbish bins and you could then encode these on the magnetic strips of cards and so
we started adding card verification values to stop forgery these are the three digit numbers
that you see on the signature strip on the card which aren’t embossed and so don’t end up being
embossed onto a sales voucher and the three-digit code is different on the magnetic strip so you
you can’t generate a workable magnetic strip forgery of a card just from visual inspection of
the surface so that came later in the late 1980s the third thread in the development of modern
electronic payment systems was the atm the automatic teller machine these appeared first
in britain in the late 1960s and by the time i became a student in the early 1970s um how
things worked is that we got punch cards i had four punch cards each worth 10 pounds that i
got every month with my bank statement so i could take these to a cash machine put them in put in
my pin and get a ten pound naughto and that was convenient because my living allowance for the
whole week was 10 pounds and so if i had needed anything more than that i had to get my savings
book and get money out of the deposit account now the early technology turned out to be
a bit flaky because the banks hadn’t done a particularly good job of encrypting the pin code
in the punch card and once people figured out how that worked they started forging punch cards
and getting money out of cash machines and so lloyd’s bank asked ibm for better cryptography and
ibm responded by supplying a cipher called lucifer 128-bit block cipher that had been developed by
a guy who had worked in identify friend of four systems in the 1950s the u.s national institute
of standards and technology then called for a data encryption standard and there was a big
political fight because the u.s national security agency demanded that the length of the key be
cut to 48 bits and eventually there was a long negotiation that it ended up being 56 bits long
this meant that by the 1990s it was possible for people to break theirs by exhaustive key search
and everybody figured that out back in the 1970s but this gave the banks a cycle system that was
good enough without it being good enough that it would tempt foreign governments to start using
it instead of the the stuff from crypto algae that they were using which the nsa knew how to
defeat as we discussed in the first lecture so um despite the fact that banking crypto started
off with a slightly suspect block cipher atm security really was the killer app this is
what brought cryptography into commerce and especially atm networking this is something
that i worked on for a few years in the 1980s and the goal then was to link up all the world’s
atms so that if you were an rbs customer you didn’t have to go to an rbs to get money out the
cash machine you could get out of out of bank of scotland too you could go to england get it out
of lies you could go to america and get it out of bank of america so the idea was that your cash
card would go with you wherever you wanted in the world and make your money available to you so
in order to do this we needed an international standard which operated at a number of levels
and at the level of concrete security policy the policy was that only the customer should ever
know their pin there should never be anybody in a bank who knows any pin other than their own
personal pin or who has the means to work it out and how we implemented this was with a set of
standard pin transactions using cryptographic devices called hardware security modules or hsms
and these keep pins and keys from individual bank staff and enable everything to be managed under
dual control and then you have hsms both at banks and also at the network switches at places like
visa which translate pins as transactions flow from one account to another and which also keep
track of which bank owes which other bank how much money for their customers taking money out of cash
machines so let’s have a look at how this works if i’ve got an rbs card and i go to barclays
bank atm in london i ask for 100 pounds out and i put in my pin it’s then encrypted as a hardware
security module um a a little potted chip which is um glued into the keypad and is tamper resistant
and that is then sent to the acquiring bank in this case barclays which has got an hsm at its
headquarters up in cheshire and there the pin is translated from the key that’s used to encrypted
by the atm so a key that’s used in the atm network which could be linked in those days or it could
be visa or mastercard or cirrus or whatever and then at the atm switch it’s decrypted from
the key that barclays used and re-encrypted using a key that royal bank uses and then it
flows through the network to rbs’s headquarters in site hill where they’ve got an hsm with
the key that knows how to verify my pin and can then send a message yes
or no back through the network now in theory the response messages should also be
authenticated using a message authentication code but many banks optimize this step out and
as a result we’ve occasionally seen attacks where um some bad people manage to impersonate
a whole bank and sometimes you see a bank fraud that costs tens of millions of pounds over
a weekend because somebody has managed to in comes in what else can go wrong well let’s look in the
detail about how pins are generated now this is the ibm system that ibm came up with in the early
1980s and made one of the international standards you start off with your primary account number
or pan and in this by international standards the first six digits of the bank’s identification
number so that that tells you five six tells you for example that this is a mastercard and
four one eight two tells you which bank it is and then you’ve got nine digits of account
number and one digit of a redundancy check giving you 16 digits so you then encrypt this
number using the bank’s pin key which is a 56 bit dez key or nowadays a 1 1 12 bit triple des key
which gives you a hex string output you then chop off the end the standard says that you can have
a pin of 4 to 12 digits most banks standardize on four digits one or two allow you to use five and
you then decimalize the result most of the banks all of the big banks in britain accept hsbc
decimalized by simply taking everything module 10 so b becomes 1 and d becomes 3 and so on
hsbc is different and they’ve got a custom customized decimalization table and so in this way
you’ve taken in a 16 digit primary account number and you’ve got out a four digit pin now there’s
a similar process used to generate the cvvs the three-digit check values uh on card magnetic
strips and on current signature strips but these use different keys and they also use the current
version number that’s beside the way for now so one of the problems that people then came
across is that some banks wanted to enable customers to change their pins so that they
could use more memorable pins and hopefully use the card more and generate more transaction
fees so ibm came up with a system whereby you store an offset between the original derived pin
and your chosen pin so here for example is our bank customer we’ve seen the primary account
number name is mr mk bond the balance is whatever and the pin offset starts at zero now if
mr bond decides to change his pin from 2213 that’s the derived pin that we saw in the previous
slide to 1979 say 1979 as his date of birth then you simply encode in the bank record
the the difference digit by digit mod 10 between the um the chosen pin and the derived pin
and this means that mr bond can use 1979 as a pin and the bank will verify the pin is 2213 using
its cryptography and everything works just fine but does it so here’s one of the early interesting technical
attacks that came up in 1989 there was one bank that needed to issue everybody with new account
numbers because they were replacing the core banking system with an incompatible one from
a different vendor and that was an enormous project that i worked on it took years and cost
hundreds of millions and so what the bank did was to get the hsm vendor to add a new command to the
api for the hsm to calculate the offset between a new generated pin and the customer’s chosen pin
they did this incidentally after i’d left so this wasn’t something i had an opportunity to
stop and what then what then went wrong was quite interesting because one of my successors pointed
out that any customer pin could now be revealed by calculating its offset from a known pin
because if i know how to calculate the offset between the natural pins and two accounts
i can not only calculate the offset between my old account and my new accounts i can
calculate the offset between my account and your account and so i can work out your pin
oops said the bank and they had to hurriedly contact the hsm vendor and get this new command
taken out of course the vendor hadn’t figured out that this new command would break the world
and that was telling because as time went on banks asked for more and more transactions to be
added to the hardware security modules transaction set until by the early 2000s leading models of
hsm had as many as 500 different transactions to cope with different ways in which different
banks worldwide did their cryptography then we started looking at it systematically mike
bond was in fact one of my research students who did his thesis clawing through hsn manuals
and figuring out all the ways in which they could be broken and this is one of the early
ways that we discovered you could do that when you set up the master key between two banks
or between a bank and a cash machine then what you do is you carry the master keys in two or three
parts uh you know giving them to separate couriers or posting them on different days so that you can
maintain the dual control policy if it’s an atm for example you might post one key to the branch
accountant on monday and then post the second key to the branch uh manager on on thursday
and that way you’ve got two separate people each having one key component in their separate
files and what happened with the system that visa had set up was that these components were combined
using the exclusive r function and nobody realized it at the time back in the 80s when this was
being designed but this was a serious mistake so let’s investigate why suppose you’ve got
a source hsm in a bank and a destination hsm for example in a cash machine so the
user that is the the program that manages um the bank’s atm fleet goes to the source hsm
and says generates a key component and the hsm dutifully prints out on an attached printer
in the security cage in the bank’s data center the first key component and it then returns
to the calling process that key component encrypted under a master key and you do that twice
and you then have two key components which you can post out to the guy in the bank branch and you’ve
got two encrypted key components kp1 and kp2 and to support this the visa cryptography had a
transaction which would enable you to take kp1 and kp2 both encrypted under a relevant
master key and then get them back again xor all together encrypted under that master key
and keys of this type would then be treated as atm master keys and they could be used for tasks
such as encrypting pins or were still encrypting the pin master key so that you could do offline
verification of customer pins so what goes wrong well the problem was this that a single operator
could feed in the same part twice and since kp1 xor kp1 is zero this means that you get out the
zero key encrypted under a master key and because it’s encrypted under this master key the hsm
will treat it as being a suitably authorized key under which you can then encrypt a pin master key
and in this way you could extract pins and you could extract pin master keys from the security
module so this was an attack a slightly subtle attack but once you’ve seen it it’s fairly obvious
and this had been in thousands of security modules sold by about a dozen different vendors to over
10 000 banks worldwide for a period of 20 years before the attack was observed and that’s
one of the bizarre things about the design of cryptographic protocols that they’re just
sufficiently subtle but you can have really devastating vulnerabilities in them which aren’t
at all obvious until of course someone spots them for the first time and then you can have a long
and expensive remediation process and this and other vulnerabilities led to a process whereby
pretty well all the world’s security modules had to have significant upgrades or
replacements during the early years of the 2000s many attacks were then found on hardware
security modules because of the complexity of the pin management that they
had been designed to support without anybody you know doing proper adversarial
attacks on them at the time back in the 1980s here for example is another attack where you
use the existence of the decimalization table in order to work out pins in a slightly more
indirect way than in the previous attack so here’s a typical pin verify command you put in
the primary account number you put in a trial pin this comes from somewhere perhaps from an atm
and it’s encrypted under some key or another but let’s disregard that as a detail from now and
you put in an encrypted pin master key that’s the pin master key that was used to turn this
primary account number into the pin 2 2 1 3. and you then put in the decimalization table and
for all banks in britain except hsbc that was just the decimalization table zero one two three four
five six seven eight nine abcdef translated to zero one two three four five six seven eight nine
zero one two three four five so what then happens inside the hardware security module is it takes
the primary account number it takes the encrypted pmk decrypts that under the appropriate master key
encrypts the pan gets the natural pin of 2 2 1 3 using the decimalization table and then
checks it against the trial pin 0 0 0 0 and are the two equal nor they aren’t so it outputs no so um how can you adapt this if you’ve got
access to this transaction how can you adapt this to workout pins well the thing to notice
is that the decimalization table is entered into the hardware security module unprotected
it’s in the clear and so what you can do is put in a malicious decimalization table all
zeros except for um a one opposite the input value of seven and what then happens is that when you
encrypt the pan the raw pins two to bd as before you decimalize at the natural pin is zero zero
zero zero you verify zero zero zero zero and you now get a yes and this yes tells you that
there isn’t a seven um in the natural pin and i think you can see where this is going and if you
sit down and work it out you’ll reckon that with something like typically 22 or 23 transactions
you can work out what a customer’s pin is and the interesting thing about this decimalization
table attack which makes it still relevant today is that first there’s many different variants
of it and when we first came up with that just about everybody that we told about it
thought up a new variant if they understood hsms at all because you can play with the
decimalization table you can play with the offset you can play with pin block formats you
can play with all the variables in the system but the general lesson from this is that this is
a differential attack on a private computation and nowadays people are doing all sorts
of fancy things with the cryptography on fully homomorphic encryption and private
set intersection and so on and so forth whereby you try and do some computations on
encrypted data now this is a very example a very early example of how this got done in the
1980s albeit using a hardware security module rather than fancy elliptic curve cryptography
and it went spectacularly wrong and why because people didn’t stop to think whether tweaking some
untrusted inputs of a computation could result in private inputs being leaked and this is something
that people are still not checking properly today and i predict that if we see fully homomorphic
encryption being used at scale in real applications we’re going to see attacks that are
somewhat reminiscent of this decimalization table attack on 1980s technology which was so obscure
that it was only discovered in the early 2000s so there we have some of the interesting
cryptographic stuff that went wrong with atms which led to competition between hsn vendors
and disputes over standardization and so on in the early 2000s but this doesn’t have very much to do
with what actually went wrong in terms of fraud on the street now during much of the 1980s there
wasn’t that much atm fraud there were occasional incidents of it when people worked with corrupt
bank insiders and then in the early 1990s we saw a growing tide of fraud which happened because
magnetic strip cars were easy to alter or to copy and gangs learned to do shoulder surfing
now back in those days the magnetic strip on your debit card didn’t have a cvv and
so an early attack was to stand outside a bank and look over somebody’s
shoulder as they put their pin in as they did a transaction and then if they
dropped the atm tickets on the ground you pick it up and in those days several banks
printed the full 16 digit number on the ticket so you knew the primary account number and
you’d observe the pin with your eyeball so you could then go and make a bank card and you
could steal money from that per guy that you just stood behind in the queue and there were gangs
learned to industrialize this there were a couple of guys who got a furniture van and they put
a video camera in it and um they had a motion sensor and this would then observe people at the
atm and capture a videotape with with timings on it and they would then go and empty out the waste
paper basket and pick out all the tickets with primary account numbers on them
they’d make up cards and they would loot the customers that wasn’t the only thing they
did but that was one of their tricks and there was a big law case where something like 2 000
people sued 13 banks for 2 million pounds back in phantom withdrawals in addition to implementation
bugs like putting 16 digits of the account number on the ticket which banks stopped quickly enough
there were insider attacks there was network diversion where somebody pretended online to be
a whole bank we later on found malware in atms and we had people social engineering pins for
stolen cards for example if you managed to steal someone’s purse and you found a couple of atm
cards in it what you would do if you were a bad person would be to phone them up and say hello
is that agatha jones it’s barclays bank here um security division uh tell me we’ve seen a
couple of transactions against your card with an off license in newcastle for over a hundred
pounds each time these look like suspicious transactions that you actually do them all
north of the customer thank you for calling my press was stolen i was just about to get round
to calling you and tell you to cancel the cards okay so the villain um that’s fine we’ve
stopped that one now just tell us your pin and i’ll go into the computer and i’ll stop
your card for you right and that worked often enough that it was a real issue and the banks
had to go out of the way to educate people what happened then um from the mid to late 1990s
is that fraud started to be industrialized using atm skimmers people defend invented devices that
would sit over the throat of an atm and would copy the magnetic strip as the card went in and it
then either had a little pinhole camera that would watch people entering their pin at the keyboard
or else even you’d have an overlay that sat on top of the pin pad itself and once people had
figured out how to make these they got various gangster associates around europe who would
actually act as their franchisees and would collect information from atms and this led to uh
growing problems with losses and eventually the banks in the late 1990s decided to start moving
to smart cars so they started designing standards and preparing for a rollout of smart card based
systems which started in 2004.
They also developed a number of centralized intrusion detection
systems which were capable of detecting fraud across atm networks worldwide one particularly
neat invention by a new york firm called fico signed up a number of banks um who would report
whenever they saw um a dodgy transaction at one of their atms and when that happened fico would put
that atm at the top of a hot atm list they kept a list of about the 40 baddest atms in in the world
at any one time and the thinking there was that if somebody stole a bunch of uh debit and credit
cards they typically go to an atm and try them out one after another to see if they worked and
so those banks that subscribed to fico’s service would pretty quickly find that their cards were
not working in that atm because it would rapidly go to the top of the hot atm list and therefore
the subscriber banks found that the criminals were throwing their cards away on the street rather
than actually using them to take money so there are a number of clever ideas like that but in
total they weren’t enough and eventually from 2004 the banks started rolling out the next
generation of technology the smart card the cards that are used nowadays for payments both
for debit card and credit card payments generally adhere to a standard called emv for european
mastercard and visa which developed this in the late 1990s and early 2000s these were deployed
from 2004 and unified to a certain extent the debit and credit card worlds one of the ways
in which this was rolled out was by means of what industry called a liability shift the
banks all changed their terms and conditions so that if there was a dispute if a
cardholder said i didn’t make that transaction then if the merchant wasn’t using emv
it would be charged to the merchant otherwise it would be charged to the cardholder
because the bank would say your card and pin were used therefore it must be your fault
you must be either negligent or complicit and so the banks believe that it would pay for
itself because they wouldn’t have to pay for fraud anymore the fraud costs would fall on the
card holder on the merchant so did things work out that way well it changed a lot of things
but not always in the ways that banks expected so um let’s think from the point of view
of the economics of the security of pins now with checks a fraud signature was null and
void and so if somebody gave you a check with a fraud signature on it that was your risk in other
words the forgery risk fell in the relying party but with pins banks managed to arrange things
in most countries that the risk would move to the user and they got away with arguing to
a complaining customer your card and pin were used so you were negligent or complicit
so what could possibly go wrong well this is the story of how fraud in the uk has evolved
since emv was initially introduced in 2004 and this is quite interesting so we’ll have a quick
look at it now and then discuss some of the components of it in the remainder of this lecture
and in the next lecture the first thing that you notice is that cardlock present fraud such as
the use of credit cards online to buy stuff absolutely shoots up this is the first takeaway
it rises very rapidly for a few years until 2008 when it falls slightly and then it starts
climbing again and it’s still climbing today the second is that counterfeit
card fraud went down initially but then it went up for several years
because um people figured out that once terminals were being used everywhere to collect
customer pins not just atms but also point-of-sale terminals and stores it was dead easy to use
false terminals to connect people’s card and pin data and then make up mag strip forgeries that
you used in those atms that still accepted them a number of the other types of fraud
fell or stayed at a relatively low level such as male non-receipt and id
theft which means impersonation mobile banking has started off since about 2015
and online banking since about 2010 and online banking started to climb uh from about 2013 or so
and we’ll look at these trends as we go through so as i just said car not present shot up
at once and counterfeit took off once the crews realized it’s easier to steal card and
pin details once pins are used everywhere and you could use mag strip fallback for several
years particularly overseas and what’s also interesting is that tamper resistance didn’t work
properly now in a later lecture we’ll discuss the mechanics of tamper resistance but let’s
start off by looking at the security economics suppose you’re running the merchant services
division of a bank and you can decide to pay an extra 10 pound per terminal to
make a million pin entry devices secure and thereby save the uk banking system overall 100
million a year in fraud would you do that decision well you would then say well what proportion of
the bank cards are issued by my bank and if your bank only issues eight percent of all the cards in
issue then you’re not going to bother doing that because the bank spends 10 million pounds and it
saves 8 million pounds so that’s not a business proposition are also issues within banks because
if the card divisions manager if you or the guy who goes and buys all these merchant terminals
and you’re going to spend 10 million of your budget so that your rival the current division
manager um saves 8 million on his then that’s an even less attractive proposition so there are
significant issues of governance around here and what we found for the first 10 years or so of chip and pin being deployed is that pin entry
devices were trivial to tab devices were claimed to be evaluated under the common criteria
which we’ll discuss later in the section on accreditation and evaluation and it turned out
that these were trivial to tap and the evaluations hadn’t complied with the requirements of the
common criteria and bank said no it wasn’t the problem and the common criteria brand owner gchq
just didn’t want to know and yet we found here for example with the this ingenico terminal was
the most commonly used pin entry device in the uk in the mid 2000s we found it was trivial to
tap because in the back of it there was a place where you could put some wicked electronics
and if you drilled a hole or you can see that paper clip going in that managed to
drop a contact onto the serial line which took the clear text pin from the pin pads
of the card and which got all the card data and transaction data coming back in the other
direction so with a wiretap like this you could steal enough information to make a magnetic strip
forgery of the card now all of a sudden there was concern in the industry because shell found that
it had to replace all its pin entry devices these were actually of a different make from trintek in
ireland and bad people managed to figure out how to put bad electronics in them and trintech in
fact went bust and um retired from the penentry device market so eventually the crooks taught the
bankers a lesson in governance of such systems and more lessons were to follow let’s look in
detail as a normal emv transaction you put your card in the pen entry device and the card says
hello i’m card for bank account number so and so and here’s some encrypted stuff and a
digital signature which proves that i am encrypted issued by such and such a bank and
the merchant then displays to the customer we’d like you to pay 59 pounds please
enter your pin and the customer enters one two three four or whatever it is and the
pin entry device then sends to the smart card um the pin is one two three four the amount
is 59 pounds blah blah blah various bits and pieces and the card then scratches its head
and um and says well okay the pin is right and here is an authorization cryptogram we’ll
look at the details later but basically it is a cryptogram that’s calculated using a
cryptographic keys is shared between the card and the card issuer so the merchant terminal
doesn’t know what that key is so it can’t verify it so it sends the transaction with the cryptogram
off to the issuer which then checks the cryptogram and checks whether the customer has got enough
money in their account if it’s above a certain floor limit and then sends an authorization back
to the merchant and that’s a busy period if the amount is below a certain threshold then the
transaction may be authorized offline without referring to the bank in order to minimize the
volume of transactions it has to be dealt with now in about 2010 some crooks in france discovered
that there was a flaw in this system and we started hearing reports of customers who had their
cards stolen and their cards had been used in transactions and the bank said that your pin must
have been used and the customers were insistent that it couldn’t possibly have been in one case
the customer had never used a pin with that card so what’s going on well we investigated and
we found um that if you have got some means of interrupting the transaction of intercepting the
transaction of doing a man-in-the-middle attack between the merchant terminal and the card for
example using a fake card or using an overlay card then what you can do is throw the pin on the
floor and tell the card that this is actually a chip and signature transaction instead
because these are allowed for some people and for cards for some countries and the only
difference is that a pin isn’t then sent so the card then gets the transaction thinking
it’s a chip and signature transaction and then works out a cryptogram and sends it back
to the bank and this is the kind of device that is used nowadays to do a no pin attack this is an
overlay sim you can buy these from taiwan and you can get a software development kit and they’re
about 180 microns thick and they’ve got smart card contacts on the top and at the bottom and
you can program them in java card so that you can manipulate transactions and you can use
them to attack cards that you’ve stolen or in other ways which we’ll describe later and
what then happens is that the card thinks it’s authenticated a chip and signature transaction
or the merchant terminal thinks that the customer enters the correct pin and if you then send
the transaction with the cryptogram to the bank the bank at least 10 years ago would happily
authorize the transaction because determining the manipulation means you have to look carefully
at the extra information returned by the card and by the terminal and doing that across complex
networks was a difficult thing to arrange so how could the no pin attack be blocked well
in theory you could block it at the terminal or the acquirer of the issuer but in practice
it usually has to be at the issuer because um with terminal tampering the incentives
for the acquirer are rather poor and although barclays introduced a fix in july
2010 they removed it in december 2010 we think because of too many false positives other
banks left their systems vulnerable to this and some of them even asked for one of our master
student thesis which investigated this to be taken down from the web instead and we told them what
they could do about that but it wasn’t until 2016 that british banks actually fixed this
and to this day we come across cases of british tourists in china who’ve had their cars stolen
where this kind of attack appears to have been carried out and the real problem here is that
the emv spec is now far too complex you’ve got a hundred plus vendors 20 000 banks millions of
merchants and everyone passes the buck and it’s really really difficult to change anything
once the system has scaled up to that size and what we’ve also found is that the api
attacks we were talking about earlier on the hsms keep on coming back so for example vs
visa defined a new hsm transaction to support emv where the idea was that you would be able to
send a cryptographic key from one hsm to another as a text string followed by a key and amazingly
they allowed the text to be variable length and this led to a simple attack where you
could encrypt text followed by 0 0 and then text followed by 0.01 and so on in order to work
out what the first byte of the key was and then by varying the length of the text you could get out
the key one byte at a time and this vulnerability turned up in all the compliant hsms worldwide
because visa had specialized and specified it and so basically what was happening is that as soon as
the hsm industry removed the api vulnerabilities the banks put them back because the governance
of the whole system was basically shot now here’s another example of how emv went wrong atms and
random numbers i said i’d look in detail about how the authentication request cryptogram is done
and here it is the terminal sends a random number this is known in the spec as the unpredictable
number we will just call it n here so the card along with the date d and the amount x and one
or two other things such as the currency code and the arqc is a mac computed using a key that
the card has and the bank also knows on nd and x so what happens if i can predict n for d if i
know what unpredictable number a given terminal will use tomorrow and if i get access
to your card i can pre-compute an arqc for that given amount and on that particular date and how did we figure this out well
we got a complaint from a guy in malta who had gone on holiday to majorca and he ate
a meal in a rather dodgy perhaps mafia-owned restaurant and the following day he found four atm
transactions on his account that he uh didn’t make and so he complained to hsbc and malta his uh his
bank and they said well our system is secure and your card and pin were used so it’s your fault
and we’re debiting you so he demanded the logs of the disputed transactions and he came to
us and this is what we found looking at the logs that the unpredictable number which you
can see in the right hand column ended up being a 17-bit constant followed by a 15-bit
counter that cycled every three minutes so we put together a test one of my postdocs
had some fun wiring up a bank card um with a clock chip and a microcontroller and some memory
so we could take fine-grained timing measurements of bank transactions that we did around atms in
the uk and we found that a bit over 40 percent of atms in the uk are also simply using counters
as unpredictable numbers and the reason for this we figured out is that in the emv spec the
testing for the unpredictable number simply says that the tester has to draw three numbers from
the device and check that they’re all different now if you’re a programmer in a hurry then using
a counter is a fast way of passing that test so how does this work out in practice well
the pre-play attack that we found in practice around europe was something that we first came
across in 2014.

Um a british sailor went into a bar in las ramblas in barcelona the big fancy
streets in downtown and he paid 33 dollars for two drinks 33 euros for two drinks and he woke
up at six in the morning with a sore head because his drink had been spiked and he then got on a
plane to paris and he then checked his account and he found that 33 000 euros had been taken from
his account at lloyds in 10 payments of 3 300. so why does a sailor have 33 000 euros while he was
working out of aberdeen on the rigs that’s why and so he went to lloyds and lloyd said your
car and pin card and pin were used so it’s your fault and so he went to a law firm and the
law firm came to us and we got the logs and we found that ten transactions had been made an hour
apart for 3 300 euros each from the same terminal but through three different banks and
with different terminal characteristics so this was clear evidence of technical tampering
and so lloyd’s basically grumbled a bit and gave him his money back and the lesson here is
that emv lacks a trustworthy user interface and so what a bad person can do is that they can
monkey with the software in an emv terminal and get it to display the wrong amount of money
to you so that you think you’re authorizing a 30-pound transaction when you actually authorize
uh 3000 pounds or that you’re actually authorizing 10 transactions when you think you’re actually
authorizing one and this can also be done by sticking one of these overlays onto the customer’s
card before you stick it in your terminal and we’ve seen a pattern of activity whereby these
kind of scams are done in red light districts all the way around europe we’ve seen them in poland
we’ve seen them in the baltic states and we have even seen them in the uk in bournemouth the
council had a dispute with a lap dancing club the spearmint rhino and the councillor came to us and
they said that multiple customers had complained of excessive car charges they’d go in and buy a
drink for the young lady for 50 quid and they’d be charged 5 000 and sometimes they woke up with
a sore head in the morning and if they complained to the bank the club just said well he was with
two girls all night and that’s what we charge the banks and the police weren’t
interested but the council was worried uh because of course if you’ve got an
establishment that starts anesthetizing people um or they’ve got full stomachs and without
medical assistance then sooner or later someone’s going to end up dead and you’ve got
a murder in your hands and so the counselor got the bournemouth echo to speak to us and they
wrote about the pre-play attack and about 20 more victims contacted the councillor and as a result
the club’s license was restricted for six months and still the police weren’t interested and we
did what we could to try and um contact the local authorities but nope um that’s not something
that they wanted to do in bournemouth or also for that matter in poland and this is actually
rather concerning now when you think about it the cards that you’ve got in your pocket um
have perhaps got a total overdraft ability several thousand pounds quite apart from any
money that you’ve got there and the banks will very often give you extra unsolicited overdrafts
so they can charge you more money for them so if you go into a red light district
establishment with three or four bank cards in your wallet it’s as if you’re going in
there with five or ten thousand pounds in cash now would you go into such an establishment carrying
five or ten thousand in actual banknotes well hey that’s one of the downsides of card payment
that if things go wrong they can go very wrong




